Bottom Line Up Front
I represent businesses facing high-stakes disputes, regulatory pressure, and contract risk. In Northern Virginia, defense, aerospace, and federal contracting companies are dealing with five legal challenges more than any others: cybersecurity compliance tied to False Claims Act exposure, bid protests and small business eligibility fights, export control and foreign access risk, workforce and trade secret disputes, and teaming agreement or organizational conflict of interest problems. These issues do not stay contained inside the legal department. They shape whether a company wins, keeps, performs, or loses federal work.
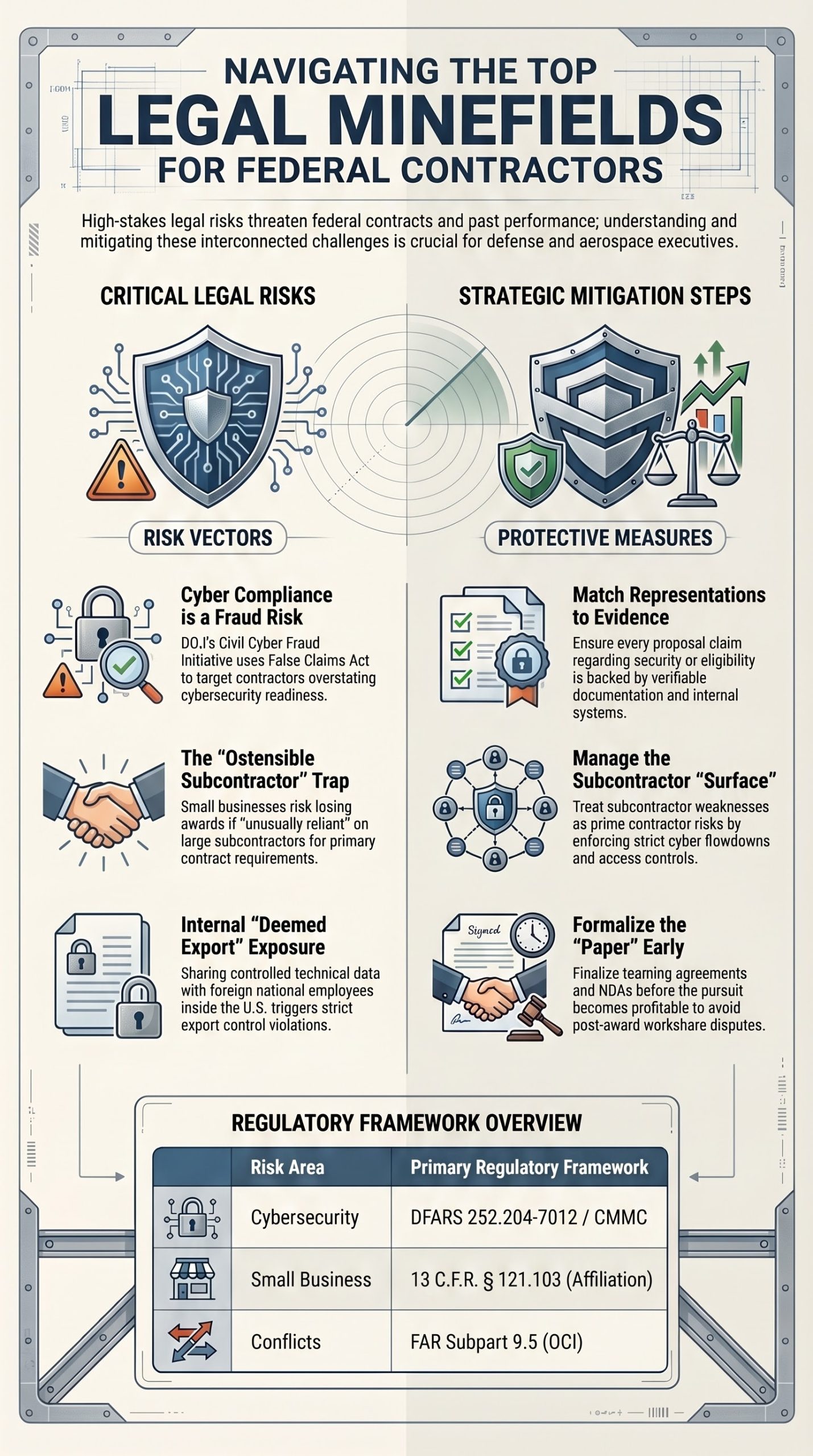
Table of Contents
- Why Northern Virginia feels this pressure first
- Cybersecurity compliance and False Claims Act risk
- Bid protests, size protests, and affiliation disputes
- Export controls, deemed exports, and foreign national access
- Cleared workforce disputes, trade secrets, and restrictive covenants
- Teaming agreements, subcontracts, and organizational conflicts of interest
- What I tell companies to do now
- Summary
- Sources
Chapter 1. Why Northern Virginia feels this pressure first
I practice in a region where federal procurement pressure is constant. Northern Virginia sits in one of the most contract-dense business environments in the country, with a heavy concentration of companies serving defense, intelligence, civilian agencies, and highly regulated mission environments. That matters because legal mistakes here move fast. A representation in a proposal can become a protest issue. A security control statement can become a payment issue. A rushed teaming arrangement can become a lawsuit after the award. The legal exposure is not abstract. It is built into how this market operates.
What makes this region different is the overlap. Northern Virginia contractors do not live in one legal lane. They usually operate across procurement law, cybersecurity obligations, employment law, trade secret protection, export controls, and subcontracting rules at the same time. A single contract pursuit can touch all of them. That is why I tell clients to stop thinking in isolated compliance buckets. The real risk is often in the seams between business development, HR, IT, program management, and legal.
Chapter 2. Cybersecurity compliance and False Claims Act risk
This is the first issue I would put on the board for almost any defense or federal contractor in Northern Virginia. Cybersecurity compliance has become a core legal risk, not simply a technical one. DFARS 252.204-7012 requires contractors and subcontractors on covered work to safeguard covered defense information and report cyber incidents. DFARS 204.75 and 252.204-7021 tie certain DoD procurements to CMMC level requirements. Those clauses are now part of how eligibility, performance, and truthfulness are judged.
The legal danger grows when companies overstate what they have done. The Department of Justice launched the Civil Cyber Fraud Initiative specifically to use the False Claims Act against contractors and grant recipients who knowingly fail to meet required cybersecurity obligations while making representations to the government. DOJ has continued to back that initiative with public settlements, including 2025 announcements involving cyber-related allegations and alleged failures to safeguard sensitive information.
The Core Legal Question
From my perspective, the core legal question is not whether your team has a policy binder. It is whether your actual systems, practices, evidence, and subcontractor controls match what your company is representing in proposals, questionnaires, assessments, and contract performance. If leadership signs the paper and operations cannot support the claim, that gap can become a fraud, termination, or past performance issue.
I also see companies underestimate subcontract flowdown exposure. DFARS 252.204-7012 expressly addresses subcontractor obligations, including cyber incident reporting and related communication to higher-tier contractors. That means prime contractors cannot treat cybersecurity risk as something that lives only inside the four walls of the prime. In this market, subcontractor weakness often becomes prime contractor pain.
Chapter 3. Bid protests, size protests, and affiliation disputes
The second major challenge is procurement challenge risk. In Northern Virginia, companies grow through small-business programs, mentor-protégé structures, joint ventures, and layered prime-sub relationships. That creates recurring disputes over size eligibility, affiliation, proposal structure, and whether a company truly qualifies for the set aside work it is chasing.
The ostensible subcontractor rule remains one of the most important pressure points for small business contractors. Under 13 C.F.R. § 121.103, a subcontractor that is not similarly situated can trigger affiliation if it performs the primary and vital requirements of the contract or if the prime is unusually reliant on it. That is not a technical foot fault. It can cost a company the award entirely. In practical terms, I look at proposal architecture, workshare, management control, staffing dependence, and who truly owns contract performance. Those facts often decide the dispute before the lawyers start arguing labels.
Bid Protest Reality
Bid protests remain a live reality as well. GAO’s fiscal year 2025 annual report shows that protests continue to be filed in substantial numbers and that GAO still tracks the most prevalent grounds for sustain decisions each year. Even where a protest is not sustained on the merits, the process can delay award, increase cost, expose proposal weaknesses, and force agencies to take corrective action. For contractors, this means proposal discipline and procurement record discipline still matter.
When I advise companies on this issue, I focus on one hard truth. Growth creates legal complexity. The more a company scales through partnerships, subsidiaries, capture arrangements, and joint pursuits, the more likely it is to trip over affiliation, eligibility, or protest issues unless governance and documentation keep pace.
Chapter 4. Export controls, deemed exports, and foreign national access
The third challenge is export control exposure, especially for defense and aerospace companies dealing with technical data, engineering support, software, source code, controlled hardware, or defense services. Many executives still think export controls start only when a shipment leaves the United States. That is too narrow. BIS states plainly that a deemed export is the sharing or release of controlled technology or source code to a foreign person within the United States. DDTC likewise warns that parties engaged in defense trade should establish and maintain an ITAR export compliance program.
This matters greatly in Northern Virginia because companies here regularly hire global talent, use mixed citizenship workforces, support classified and unclassified programs in parallel, and collaborate with teammates across corporate boundaries. The legal issue is often not intentional wrongdoing. It is weak controls over access to technical data, source code, test environments, engineering repositories, drawings, or defense services. One careless permission setting or one informal collaboration workflow can create serious exposure.
Operational Compliance Requirements
I tell clients that export control compliance has to be operational, not ceremonial. DDTC’s compliance guidance points companies toward structured internal controls, policies, and training. BIS guidance likewise emphasizes concepts and release rules for deemed export licensing. In real terms, that means companies need role based access, classification discipline, visitor controls, onboarding review, offboarding control, and clean documentation showing who had access to what and why.
Chapter 5. Cleared workforce disputes, trade secrets, and restrictive covenants
The fourth major challenge is workforce conflict. Northern Virginia companies compete aggressively for cleared and highly specialized employees. That environment creates legal stress around hiring, departures, background screening, confidentiality, solicitation risk, and misuse of sensitive business information.
Security clearance related hiring decisions add another layer. EEOC states that some defense contractors require security clearances for certain roles and that clearance determinations generally must be processed without regard to race, religion, or national origin, even though national security related exceptions can affect review under equal employment opportunity statutes. That means employers in this market must navigate both legitimate security driven requirements and anti discrimination obligations at the same time.
Virginia Trade Secret Protection
On the proprietary information side, Virginia’s Uniform Trade Secrets Act gives companies meaningful tools. Virginia law defines trade secrets, allows injunctive relief and damages, requires courts to preserve the secrecy of alleged trade secrets through measures such as protective orders and sealed proceedings, and imposes a three year limitations period for misappropriation claims. For contractors, this matters because employee movement in this market is constant. If your company has not identified what is actually secret, who has access, and how you protect it, trade secret litigation becomes harder and more expensive fast.
Virginia also limits noncompetes for low wage employees, while expressly preserving nondisclosure protections aimed at trade secrets and proprietary or confidential information. That statutory structure is important. It means employers cannot lazily rely on overbroad restrictions and assume they are protected. They need tailored confidentiality, access, return of property, and trade secret controls that actually fit the workforce and the work.
Chapter 6. Teaming agreements, subcontracts, and organizational conflicts of interest
The fifth challenge is the one many companies underestimate at the capture stage and regret later. Teaming agreements, workshare understandings, proposal collaboration, consultant access, and subcontract negotiations create fertile ground for disputes after an award decision or after a loss. Northern Virginia’s contracting economy runs heavily on partnerships. That means legal exposure often starts before the contract is awarded.
Many companies treat teaming agreements as relationship documents rather than risk documents. That is a mistake. If the agreement is vague on exclusivity, proposal contributions, data ownership, pricing assumptions, workshare expectations, and what happens if the parties cannot agree on a subcontract, the business team often believes it has a deal when the paper does not actually protect it. I regularly tell companies that a weak teaming structure is an invitation to post award conflict. That conflict can take the form of breach claims, lost opportunity claims, or internal operational breakdowns that poison performance. This is especially true when the subcontractor was central to the pursuit strategy or proposal.
Organizational Conflicts of Interest
Organizational conflicts of interest add another layer. FAR Subpart 9.5 establishes the framework for identifying, evaluating, and resolving organizational conflicts of interest. Agencies and contractors alike must assess whether a company has unequal access to information, has helped set biased ground rules, or faces impaired objectivity in future work. In Northern Virginia, where contractors often support acquisition support, advisory, engineering, and operational roles across related mission spaces, OCI analysis is not theoretical. It can block a future bid, require mitigation, or limit a contractor’s role.
For me, the key legal insight is simple. Capture enthusiasm often outruns legal discipline. Companies are so focused on winning that they fail to define how the relationship works if they do win. That is where litigation and major business loss often begin.
Chapter 7. What I tell companies to do now
When I counsel defense, aerospace, and federal contracting companies in this region, I do not start with generic compliance slogans. I start with proof.
First, match every material representation to evidence. If your company says it is compliant, eligible, small, secure, or properly structured, there should be real documentation to back up that claim.
Second, treat subcontractors and teammates as part of your legal exposure surface. Cyber flowdowns, performance dependence, access to information, and workshare structure all matter.
Third, protect data with the same seriousness you protect contract vehicles. Technical data, source code, pricing, pipeline intelligence, and capture strategy are often the real assets at risk.
Fourth, tighten the paper before the relationship becomes profitable. That means teaming agreements, NDAs, access controls, employee agreements, and subcontract terms need to be built for conflict, not for optimism.
Fifth, do not wait for a protest, subpoena, internal complaint, or data incident before involving counsel. In this market, delay usually makes the legal record worse, not better.
Summary
In my view, the top five legal challenges for defense, aerospace, and federal contracting companies in Northern Virginia are clear.
Cybersecurity compliance has become contract truthfulness risk.
Bid protests and small business eligibility disputes can erase an award.
Export control failures can grow out of routine collaboration if access is not controlled.
Workforce competition can become trade secret and employment law conflict.
Teaming and OCI problems can destroy opportunities before or after award.
These are not side issues. They are central business risks for companies that want to grow in the federal market. The contractors that perform best over time are usually not the ones with the most optimistic capture language. They are the ones whose contracts, systems, workforce controls, and internal evidence can withstand scrutiny when pressure arrives.
Schedule a Consultation
If your Northern Virginia defense, aerospace, or federal contracting company faces cybersecurity compliance challenges, bid protest risk, export control concerns, workforce disputes, or teaming agreement conflicts, Shin Law Office provides experienced representation protecting federal contract interests and navigating complex procurement regulations.
Call 571-445-6565 or visit our contact page
Author: Anthony I. Shin, Esq.
Firm: Shin Law Office
Location: Leesburg, Virginia
Sources
Bureau of Industry and Security. (n.d.). Deemed exports. U.S. Department of Commerce. Retrieved April 19, 2026, from https://www.bis.doc.gov/index.php/policy-guidance/deemed-exports
Bureau of Industry and Security. (n.d.). What is a deemed export? U.S. Department of Commerce. Retrieved April 19, 2026, from https://www.bis.doc.gov/index.php/documents/regulation-docs/412-part-734-scope-of-the-export-administration-regulations/file
Code of Federal Regulations. (2026). 13 C.F.R. § 121.103, How does SBA determine affiliation? Electronic Code of Federal Regulations. Retrieved April 19, 2026, from https://www.ecfr.gov/current/title-13/chapter-I/part-121/subpart-A/subject-group-ECFR2a69e97634dd7c1/section-121.103
Code of Virginia. (n.d.). Chapter 26. Uniform Trade Secrets Act. Virginia Law. Retrieved April 19, 2026, from https://law.lis.virginia.gov/vacode/title59.1/chapter26/
Code of Virginia. (n.d.). § 59.1-336. Short title and definitions. Virginia Law. Retrieved April 19, 2026, from https://law.lis.virginia.gov/vacode/title59.1/chapter26/section59.1-336/
Code of Virginia. (n.d.). § 59.1-339. Preservation of secrecy. Virginia Law. Retrieved April 19, 2026, from https://law.lis.virginia.gov/vacode/title59.1/chapter26/section59.1-339/
Code of Virginia. (n.d.). § 59.1-340. Statute of limitations. Virginia Law. Retrieved April 19, 2026, from https://law.lis.virginia.gov/vacode/title59.1/chapter26/section59.1-340/
Code of Virginia. (n.d.). § 40.1-28.7:8. Covenants not to compete prohibited; exceptions. Virginia Law. Retrieved April 19, 2026, from https://law.lis.virginia.gov/vacode/title40.1/chapter3/section40.1-28.7:8/
Defense Federal Acquisition Regulation Supplement. (2025). 252.204-7012 Safeguarding covered defense information and cyber incident reporting. Acquisition.gov. Retrieved April 19, 2026, from https://www.acquisition.gov/dfars/252.204-7012-safeguarding-covered-defense-information-and-cyber-incident-reporting
Defense Federal Acquisition Regulation Supplement. (2025). 252.204-7021 Contractor compliance with the Cybersecurity Maturity Model Certification level requirements. Acquisition.gov. Retrieved April 19, 2026, from https://www.acquisition.gov/dfars/252.204-7021-cybersecurity-maturity-model-certification-requirements
Defense Federal Acquisition Regulation Supplement. (2025). Subpart 204.75 Cybersecurity Maturity Model Certification. Acquisition.gov. Retrieved April 19, 2026, from https://www.acquisition.gov/dfars/subpart-204.75-cybersecurity-maturity-model-certification
Equal Employment Opportunity Commission. (n.d.). Pre-employment inquiries and security/background checks for applicants who are members of certain religious or ethnic groups. U.S. Equal Employment Opportunity Commission. Retrieved April 19, 2026, from https://www.eeoc.gov/laws/guidance/pre-employment-inquiries-and-securitybackground-checks-applicants-who-are-members
Federal Acquisition Regulation. (2026). Subpart 9.5 Organizational and consultant conflicts of interest. Acquisition.gov. Retrieved April 19, 2026, from https://www.acquisition.gov/far/subpart-9.5
Government Accountability Office. (2025, December 12). GAO bid protest annual report to Congress for fiscal year 2025 (GAO-26-900695). Retrieved April 19, 2026, from https://www.gao.gov/products/gao-26-900695
U.S. Department of Justice. (2021, October 6). Deputy Attorney General Lisa O. Monaco announces new Civil Cyber Fraud Initiative. Retrieved April 19, 2026, from https://www.justice.gov/opa/pr/deputy-attorney-general-lisa-o-monaco-announces-new-civil-cyber-fraud-initiative
U.S. Department of Justice. (2025, September 30). Georgia Tech Research Corporation agrees to pay $875,000 to resolve civil cyber fraud litigation. Retrieved April 19, 2026, from https://www.justice.gov/opa/pr/georgia-tech-research-corporation-agrees-pay-875000-resolve-civil-cyber-fraud-litigation
U.S. Department of Justice. (2025, May 1). Raytheon Companies and Nightwing Group to pay $8.4 million to resolve False Claims Act allegations relating to cybersecurity requirements in Department of Defense contracts. Retrieved April 19, 2026, from https://www.justice.gov/opa/pr/raytheon-companies-and-nightwing-group-pay-84-million-resolve-false-claims-act-allegations
U.S. Department of State, Directorate of Defense Trade Controls. (n.d.). Getting and staying in compliance with the ITAR. Retrieved April 19, 2026, from https://www.pmddtc.state.gov/ddtc_public/ddtc_public?id=ddtc_public_portal_itar_landing
U.S. Department of State, Directorate of Defense Trade Controls. (n.d.). ITAR compliance. Retrieved April 19, 2026, from https://www.pmddtc.state.gov/ddtc_public/ddtc_public?id=ddtc_kb_article_page&sys_id=c8c23ed8dbbf13001371c793bf961957
U.S. Department of State, Directorate of Defense Trade Controls. (n.d.). Understand the ITAR. Retrieved April 19, 2026, from https://www.pmddtc.state.gov/ddtc_public/ddtc_public?id=ddtc_kb_article_page&sys_id=24d528fddbfc930044f9ff621f961987




